
Blogs
Attaining a Security SPD
In the second article in our Security SPD series, Michael Brooke offers tips to help partners gain the insight track from start to finish.
Microsoft 365 E5 is the most comprehensive suite offered by Microsoft, integrating advanced security, compliance, and IT management features. It is designed to help businesses consolidate multiple solutions into one, thereby reducing costs and simplifying IT management.
Over the next hour our session experts will guide you through the Microsoft E5 solution, how to deploy best practices that safeguard data and streamline compliance.
You’ll learn how implementing Microsoft E5 can help to reduce licensing costs by up to 60% and improve IT management efficiencies.
Watch the full webinar below, read on for key takeaways and download the presentation deck for future reference.
![]()
Andrew Aldridge
Pre-sales Technical Specialist, Crayon Channel APAC
Michael Brooke
Solution Architect, Crayon Channel APAC
![]()

Security Specialist, Microsoft Australia

Security Consultant, Microsoft Australia
![]()
Microsoft E5 provides the means to simplify security practices in five significant ways:
Juggling multiple standalone security tools can be both expensive and complex. By switching to Microsoft 365 E5, you get an all-in-one, integrated suite which can greatly reduce licensing costs and contribute to less overall management complexity.
Defender for Office 365 and Defender for Endpoint come with built-in automated investigation and response features. These tools take over repetitive security tasks, freeing your team to focus on higher-priority issues. Plus, automated responses mean threats are dealt with faster than ever.
Using Entra ID’s risk-based conditional access, you can strike the perfect balance between security and convenience. This feature evaluates the risk of each login attempt and adjusts security measures accordingly, keeping data safe without frustrating users.
Poor organisational culture will eat your cybersecurity strategy for breakfast. Tools like attack simulation training in Defender for Office 365 can create opportunities to wrap ongoing services around employee education and simulated training for improved frontline understanding of common tactics such as phishing.
For technical users, the struggle to manage the complex nature of security is real. The leaner the team, the greater the need to do more with less, while avoiding increased concern and stress about cutting corners or missing critical incidents.Microsoft 365 E5 is like having a Swiss Army knife for security and compliance. Its unified dashboard provides a clear view of threats across the IT environment, while risk-based conditional access and automated remediation help small or less specialised security teams keep pace with changing techniques and tools used by attackers.
Plus, the features in the E5 suite are ideal for reducing manual processes related to regulatory and compliance demands.
![]()
Microsoft 365 E5 is available in two tiers in Australia: P1 and P2, each tailored to different organisational needs.
This provides robust security and compliance features, including core tools like Microsoft Defender for Office 365 and advanced threat protection capabilities. It’s a solid choice for organisations seeking essential protection and management features without extensive customisation or advanced analytics.
P1 balances affordability and functionality, making it an ideal jump-on plan for SMB customers with lower maturity in their overall approach to security, and/or where there is insufficient technical expertise to manage and maintain more complex security configurations.
This includes all P1 features but adds more sophisticated capabilities, such as advanced risk-based conditional access, automated investigation and remediation, insider risk management, and advanced eDiscovery.
P2 is designed for businesses with higher security and compliance demands, such as those in regulated industries or with a need for detailed forensic insights.
The choice of plan depends on the client’s specific requirements. P2, however, suits customers with a heightened focus on compliance and proactive threat management. For clients managing sensitive data or working in industries like healthcare or finance, P2 provides the depth of protection and analytics required to meet stringent security and regulatory needs.

Blogs
In the second article in our Security SPD series, Michael Brooke offers tips to help partners gain the insight track from start to finish.

Blogs
In the first of a 3-part series, Michael Brooke explains why the buying signals from the market make Security SPD attainment worth a close look for partners.

Training
The sun is setting on Microsoft Project Online, with Microsoft announcing it will be fully retired on September 30, 2026. Get the need-to-know information to plan for this change and position alternatives with your customers.

Press Release
Crayon wins 2026 Nitro APAC Reseller of the Year, with team leaders honoured for supporting partners and accelerating digital document adoption.

Press Release
Crayon's Warren Nolan and Harith Ramotheram have earned recognition in the 2026 CRN Asia Channel Leaders list for driving partner growth and innovation in our region.

Blogs
Learn how Microsoft’s strategic Copilot for All framework combines with Crayon’s inhouse AI expertise to drive practice development and revenue growth for partners.

On Demand Webinars
Watch the on‑demand webinar on turning data risk into revenue. Learn how partners use data protection maturity models to drive recurring revenue and customer trust.

On Demand Webinars
Join our team for a business and technical deep dive into the Microsoft Security SPD and why attaining it is great for business.

Business
AvePoint Partner onboarding content packs are now available from Crayon to help fast track confidence and success for your team.

On Demand Webinars
Our latest On-Demand webinar provides a practical, execution focused walk through the full Copilot partner journey, from early adoption to advanced scenarios.

Training
In our latest webinar, our in-house Modern Work experts Jye Wong and Ksenia Turner will run you through a practical refresher on Solution Partner Designations; what they are, why they matter and how to get started.
Guides and eBooks
As SMBs mature in the Data Protection lifecycle, they need help to optimise spend, reduce the compliance burden and ensure results align to business objectives. The third installment of our Data Protection Playbook series provides practical guidance for partners on how to address emerging pressure and connect ongoing investment to measurable business value.
Training
Copilot Agents: what are they and how do they differ from AI assistants and chatbots? Our in-house Copilot expert Ksenia Turner explains the use cases and service opportunities for partners.

Blogs
Fragmented data protection systems and processes create compliance proof-gaps for SMB customers. Scott Hagenus, Director, Cybersecurity here at Crayon explains.

Guides and eBooks
How can partners help their SMB customers to move from silos of security and continuity to a more cohesive, measurable and insurable data protection framework? The second edition in our Data Protection Playbook series maps out their journey, and yours.

Blogs
As cybersecurity and continuity converge in platforms and in practice, partners need new playbooks to address modern Data Protection standards. Our in-house cybersecurity pre-sales lead, Michael Brooke explains why.

Insights
Data Protection priorities are shifting for SMBs. Ramp up your ability to respond with curated insights, articles and resources to help you guide every customer conversation with confidence.

Insights
All the latest insights, articles and resources on M365 Copilot, curated into one place.

Partner Spotlight
Bigfish Technology saved AU$20,000 on its annual Microsoft licensing after one call with Crayon and has since built a strong partnership that enabled Bigfish to get access to Crayon’s expertise and vendor ecosystem.

Blogs
From rethinking backup to governance frameworks and behavioural analytics, what's involved in building a complete Data Protection strategy for SMB customers?
Insights
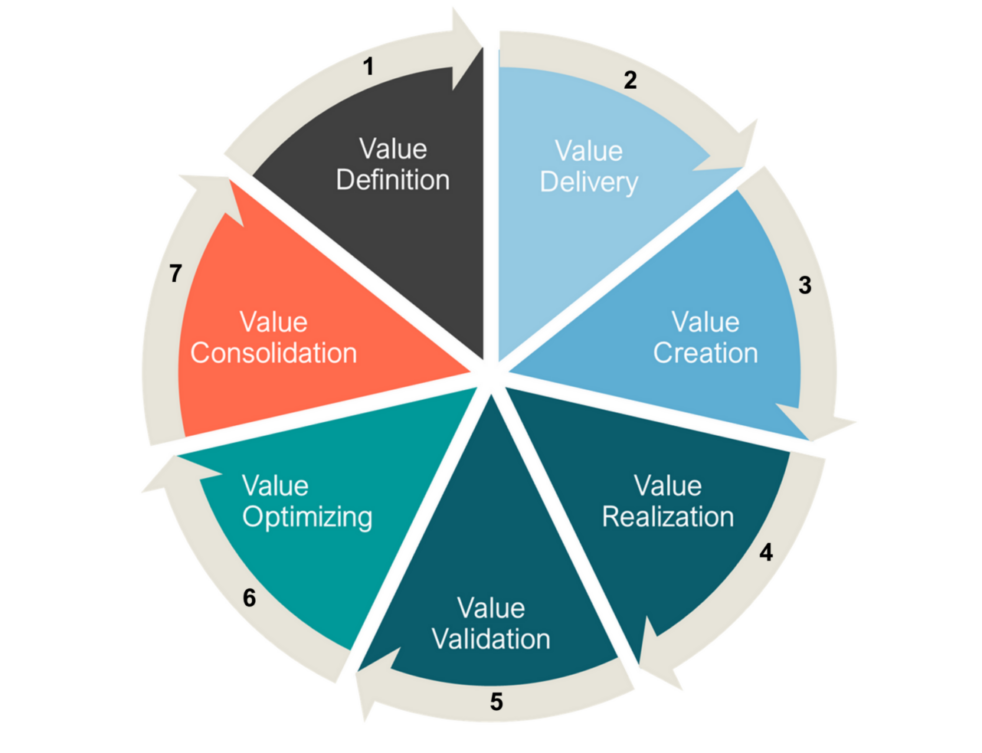
We explore the evolution of Microsoft's channel strategy over the past ten years, and what can be learned by viewing it through a Value Cycle lens.

Guides and eBooks
The Microsoft Fabric Partner Guide curates our recent articles, videos and resources to accelerate Crayon partner learning.

Sales and Marketing
Pricing models, service definitions and competitive accelerators. Our latest webinar breaks down how to build a successful MSSP business.
Guides and eBooks
Mission essentials for winning data protection business in education, healthcare, retail and manufacturing.
Guides and eBooks
Partners, get your Bond on! Our Cyber Operatives Field Guide breaks down five cybersecurity missions to foil would-be cybercriminals.

Insights
The Essential Eight security framework is a pragmatic and clear-cut way for partners to get their customers on the right track when it comes to improved cybersecurity posture.

Blogs
An explosion in ransomware attacks has fueled a nationwide review of the issue, as concern rises that secret payoffs add increased fuel to the cybercrime fire.
Blogs
Crayon cloud security assessments help partners lock down M365 and Azure environments and build profitable cybersecurity practices. Learn how.

Connect Data Protection to strategic objectives via this Whitepaper

What are the most critical business objectives and solution adoption priorities for SMBs in our region? Download the latest Forrester study to find out!

Our APAC channel business is now part of a global organisation. That means there is a whole new world of value on offer for our partners. We can help you to tap into all of it.