
On Demand Webinars
Copilot Partners: Unlock your opportunities
Our latest On-Demand webinar provides a practical, execution focused walk through the full Copilot partner journey, from early adoption to advanced scenarios.
Partners, get your Bond on! Our Cyber Operatives Field Guide breaks down five cybersecurity missions to foil would-be cybercriminals.
Much like the high-stakes world of international superspies, modern businesses must navigate a landscape rife with digital threats that can spell disaster.
To truly master the cyber domain requires more than just cutting-edge technology. You’ll need strategies that ensure you can bounce back in the face of persistent attack types. Resilience is your best response.
Our latest eBook ‘The Cyber Operatives Field Guide’ offers detailed hypothetical attack briefings drawn from real world events to help you identify and counter common scenarios across data, identity, endpoints, and cloud platforms.
You’ll meet a host of devious archetypes and learn how partners and their customers can unite to combat them at every turn. Each mission breaks down the techniques, tools and practices of attackers, along with response parameters for partners and customers and the must-haves to include in every technical go-bag.
PLUS: a raft of quotes and references to the best of the best in the crime fighting world. See how many you can spot!
Here’s a sneak peek at what each mission entails:

Cyber adversaries often rely on social reconnaissance and pretexting to manipulate employees into unwittingly divulging sensitive information. Find out how cool-as-ice Izzy Salander weeds out an invasive element that’s using open-source intelligence to craft convincing personas and run spear-phishing attempts.
A hacker for hire that never sleeps, exists on Red Bull, chocolate-coated coffee beans and the thrill of illicit financial gain has cracked open an LDAP server. Unauthorised access to a treasure trove of organisational data is within his grasp. Will Miracle Max uncover the exploit and foil this threat actor?
From public charging stations to attempting to exploit MSP environments to tunnel through to customers, endpoints are prime targets for malware and ransomware attacks. In this mission, our agents are up against the coordinated efforts of a state-sponsored hacking group and must stop them from exfiltrating and ransoming high-value intellectual property via a software supply chain attack.
A devious threat actor has launched a Magecart attack to target e-commerce platforms and web browsers, targeting $32 million in payment transactions. Effective Level 3 resilience parameters will be needed to deny this crook a huge payload.
A poor cybersecurity culture leaves a back door open to malicious outsiders who will take advantage of any opportunity to find your weakest link. Human behaviour has the potential to render even the most comprehensive cyber resilience strategy worthless. Find out how to help your customers make every employee an allied agent in the cybersecurity mission.
These missions, should you choose to accept them, can help you learn to take on cybersecurity threats with the finesse of the best technical wizards in Q branch.
Good luck and remember… building true operational and cyber-resilience is your best response.

On Demand Webinars
Our latest On-Demand webinar provides a practical, execution focused walk through the full Copilot partner journey, from early adoption to advanced scenarios.
Blogs
Catch our comprehensive summary of the highlights from Microsoft Ignite 2025, combined with the resources and links you need to dig into the detail!

Training
In our latest webinar, our in-house Modern Work experts Jye Wong and Ksenia Turner will run you through a practical refresher on Solution Partner Designations; what they are, why they matter and how to get started.

Sales and Marketing
Business leaders don't live in the tools. They live in the outcomes. The metrics they care about most are not always limited to compliance and risk. So how do you connect data protection to the big-ticket objectives, when they're less obvious? Our in-house pre-sales expert, Michael Brooke explains.
Guides and eBooks
As SMBs mature in the Data Protection lifecycle, they need help to optimise spend, reduce the compliance burden and ensure results align to business objectives. The third installment of our Data Protection Playbook series provides practical guidance for partners on how to address emerging pressure and connect ongoing investment to measurable business value.
Training
Copilot Agents: what are they and how do they differ from AI assistants and chatbots? Our in-house Copilot expert Ksenia Turner explains the use cases and service opportunities for partners.

Blogs
Fragmented data protection systems and processes create compliance proof-gaps for SMB customers. Scott Hagenus, Director, Cybersecurity here at Crayon explains.

Guides and eBooks
How can partners help their SMB customers to move from silos of security and continuity to a more cohesive, measurable and insurable data protection framework? The second edition in our Data Protection Playbook series maps out their journey, and yours.

Sales and Marketing
Ever wonder why a pitch has some IT Managers leaning forward, while others glaze over? Michael Brooke, Cybersecurity Pre-Sales Lead offers some insight on how to tune your approach to chime with different technical mindsets.

Vendor Announcements
Copilot for Business has landed at Microsoft Ignite 2025, levelling the GenAI playing field for SMB customers. Learn all about it from our man on the ground, Andreas Bergman.

Press Release

Press Release

Blogs
As cybersecurity and continuity converge in platforms and in practice, partners need new playbooks to address modern Data Protection standards. Our in-house cybersecurity pre-sales lead, Michael Brooke explains why.

Guides and eBooks
What triggers an SMB customer to begin exploring their need for better Data Protection? The first of our four Data Protection Playbooks for partners breaks down how to position and win in the Pre-Adoption and Exploration stage.

Insights
Data Protection priorities are shifting for SMBs. Ramp up your ability to respond with curated insights, articles and resources to help you guide every customer conversation with confidence.

Partner Spotlight
In this Partner Spotlight, Acceltech Managing Director Ivy Tarrobago shares how Crayon’s responsive support enhances client outcomes and business growth.

Whitepapers
Data Protection is a must for all SMBs but how can partners align solution investment with critical business objectives? Our latest paper shows you how.

Press Release
Crayon has been recognised with a huge double win at the CRN Channel Asia awards ceremony.

Insights
All the latest insights, articles and resources on M365 Copilot, curated into one place.

Insights
SMB customers are storing greater volumes of sensitive data in more places than ever. Secure backup and recovery practices are essential to how they protect it.

Partner Spotlight
Bigfish Technology saved AU$20,000 on its annual Microsoft licensing after one call with Crayon and has since built a strong partnership that enabled Bigfish to get access to Crayon’s expertise and vendor ecosystem.

Insights
Insider risk is a subtle and continuous challenge for SMB customers. Turn it into a manageable and quantifiable aspect of their Data Protection strategy.

Blogs
From rethinking backup to governance frameworks and behavioural analytics, what's involved in building a complete Data Protection strategy for SMB customers?
Insights
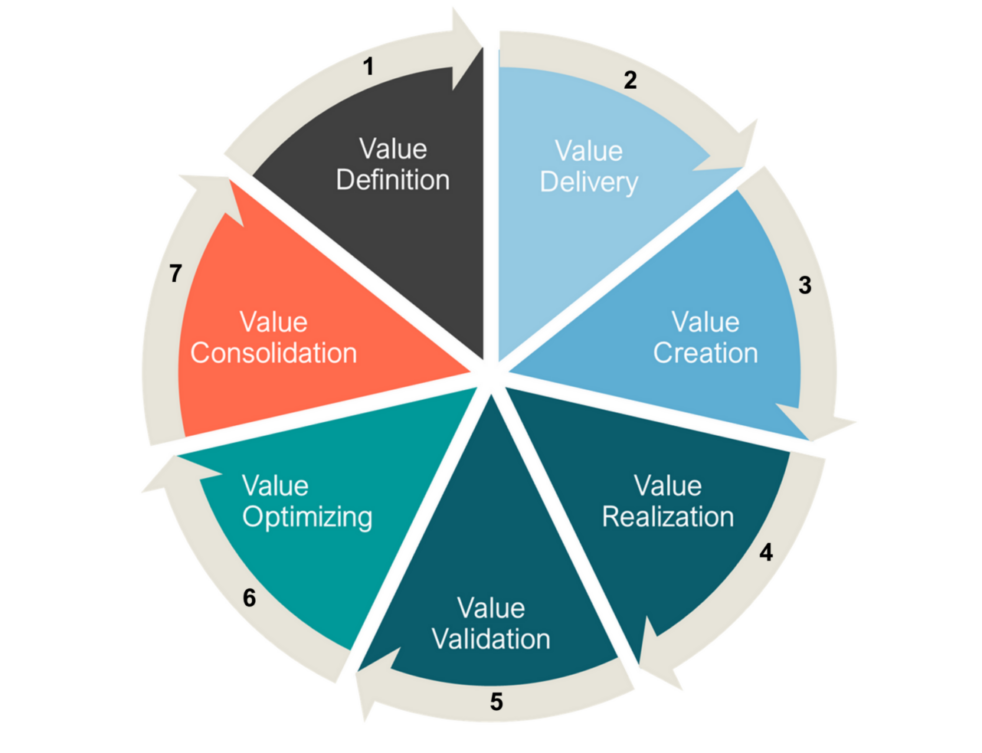
We explore the evolution of Microsoft's channel strategy over the past ten years, and what can be learned by viewing it through a Value Cycle lens.

Guides and eBooks
The Microsoft Fabric Partner Guide curates our recent articles, videos and resources to accelerate Crayon partner learning.

Blogs
An explosion in ransomware attacks has fueled a nationwide review of the issue, as concern rises that secret payoffs add increased fuel to the cybercrime fire.

Webinars Series
How do security assessments empower your cybersecurity practice to respond to the rise of AI? Find out!


Case Studies
Essential Eight Compliance can be tough to maintain for partners and customers. Learn how Airlock simplified the challenge for one MSP, and delivered faster time to value.

Press Release

Podcast
Cybersecurity experts from Crayon, SMX and Red Sift cover the realities of the complex threat landscape and how partners can respond.

Company Announcements

Press Release
Empowering Partners, MSPs and ISVs with best-in-class protective DNS security solutions

Blogs
Crayon cloud security assessments help partners lock down M365 and Azure environments and build profitable cybersecurity practices. Learn how.


Connect Data Protection to strategic objectives via this Whitepaper

What are the most critical business objectives and solution adoption priorities for SMBs in our region? Download the latest Forrester study to find out!

Our APAC channel business is now part of a global organisation. That means there is a whole new world of value on offer for our partners. We can help you to tap into all of it.