
Blogs
Attaining a Security SPD
In the second article in our Security SPD series, Michael Brooke offers tips to help partners gain the insight track from start to finish.
The Australian Cyber Security Centre (ACSC) continues to release an alarming series of alerts about escalating cyber threats. The ACSC recommends Australian organisations should: “urgently adopt an enhanced cyber security posture. Organisations should act now and follow ACSC’s advice to improve their cyber security resilience in light of the heightened threat environment.”
The ACSC encourages organisations to implement ACSC’s flagship security framework – called the Essential Eight. It urges organisations to: “review the Essential Eight and prioritise remediating any identified gaps in Essential Eight maturity.”
For SMBs at the start of their cyber security journey, it can seem like a long, complex and costly road. For many SMBs, it can be difficult to know where to start, and also to know how much cyber security is enough.
That’s where the Essential Eight comes in. It removes a lot of the concern and complexity for customers, because ACSC cyber security experts have done most of the thinking and planning for you. They’ve identified the major threats and listed actions to mitigate them. For cost-conscious SMBs, the good news is the Essential Eight is free expert consultancy.
For partners, the Essential Eight provides an easy-to-follow plan that helps you to identify where your services can quickly and cost-effectively implement baseline security mitigation. Each of the Essential Eight mitigations is a building block on the road to beefing up security.
The Essential Eight mitigation strategies are grouped under 3 major themes:
The three major themes and eight mitigation strategies of the Essential Eight are summarised in the table below.
| Theme | Mitigation strategy |
| Prevent Attacks | Application Control
Patch Applications Configure Microsoft Office Macros User Application Hardening |
| Limit Extent of Attacks | Restrict Administrative Privileges
Patch Operating Systems Multi-factor Authentication |
| Recover Data & System Availability | Regular Backups |
The beauty of the Essential Eight is it breaks up all the potential security threats and related mitigations into eight digestible chunks and describes in detail what organisations need to do to strengthen their defences against the threats.
SMBs are given a list of actions and metrics for each of the eight mitigations to reduce their risk from cybercrime. When SMBs implement the recommended security standards for each of the eight mitigation strategies, they start to build a joined-up security strategy.
This can then be used as the SMB’s cyber security roadmap. It serves as an action plan and a security policy document that can be understood and communicated to all staff in the business. And importantly, it can serve as a transparent checklist that business leaders can review to ensure their SMB is taking the right steps to keep cybercrime at arm’s length. The Essential Eight security checklist can also be audited as part of compliance processes.
The Essential Eight is the outcome of some serious thinking by highly talented ACSC cyber security experts and provides a practical and realistic starting point for many SMBs.
For partners, Crayon has a service offering that can help you get your customers on the right track. Our Essential Eight maturity assessment offering is ideal whether you have an existing cybersecurity practice or need new ways to respond to increased concern from your SMB customers.
Learn More about how we can help.

Blogs
In the second article in our Security SPD series, Michael Brooke offers tips to help partners gain the insight track from start to finish.

Blogs
In the first of a 3-part series, Michael Brooke explains why the buying signals from the market make Security SPD attainment worth a close look for partners.

Training
The sun is setting on Microsoft Project Online, with Microsoft announcing it will be fully retired on September 30, 2026. Get the need-to-know information to plan for this change and position alternatives with your customers.

Press Release
Crayon wins 2026 Nitro APAC Reseller of the Year, with team leaders honoured for supporting partners and accelerating digital document adoption.

Press Release
Crayon's Warren Nolan and Harith Ramotheram have earned recognition in the 2026 CRN Asia Channel Leaders list for driving partner growth and innovation in our region.

Blogs
Learn how Microsoft’s strategic Copilot for All framework combines with Crayon’s inhouse AI expertise to drive practice development and revenue growth for partners.

On Demand Webinars
Watch the on‑demand webinar on turning data risk into revenue. Learn how partners use data protection maturity models to drive recurring revenue and customer trust.

On Demand Webinars
Join our team for a business and technical deep dive into the Microsoft Security SPD and why attaining it is great for business.

Business
AvePoint Partner onboarding content packs are now available from Crayon to help fast track confidence and success for your team.

On Demand Webinars
Our latest On-Demand webinar provides a practical, execution focused walk through the full Copilot partner journey, from early adoption to advanced scenarios.

Training
In our latest webinar, our in-house Modern Work experts Jye Wong and Ksenia Turner will run you through a practical refresher on Solution Partner Designations; what they are, why they matter and how to get started.
Guides and eBooks
As SMBs mature in the Data Protection lifecycle, they need help to optimise spend, reduce the compliance burden and ensure results align to business objectives. The third installment of our Data Protection Playbook series provides practical guidance for partners on how to address emerging pressure and connect ongoing investment to measurable business value.
Training
Copilot Agents: what are they and how do they differ from AI assistants and chatbots? Our in-house Copilot expert Ksenia Turner explains the use cases and service opportunities for partners.

Blogs
Fragmented data protection systems and processes create compliance proof-gaps for SMB customers. Scott Hagenus, Director, Cybersecurity here at Crayon explains.

Guides and eBooks
How can partners help their SMB customers to move from silos of security and continuity to a more cohesive, measurable and insurable data protection framework? The second edition in our Data Protection Playbook series maps out their journey, and yours.

Blogs
As cybersecurity and continuity converge in platforms and in practice, partners need new playbooks to address modern Data Protection standards. Our in-house cybersecurity pre-sales lead, Michael Brooke explains why.

Insights
Data Protection priorities are shifting for SMBs. Ramp up your ability to respond with curated insights, articles and resources to help you guide every customer conversation with confidence.

Insights
All the latest insights, articles and resources on M365 Copilot, curated into one place.

Partner Spotlight
Bigfish Technology saved AU$20,000 on its annual Microsoft licensing after one call with Crayon and has since built a strong partnership that enabled Bigfish to get access to Crayon’s expertise and vendor ecosystem.

Blogs
From rethinking backup to governance frameworks and behavioural analytics, what's involved in building a complete Data Protection strategy for SMB customers?
Insights
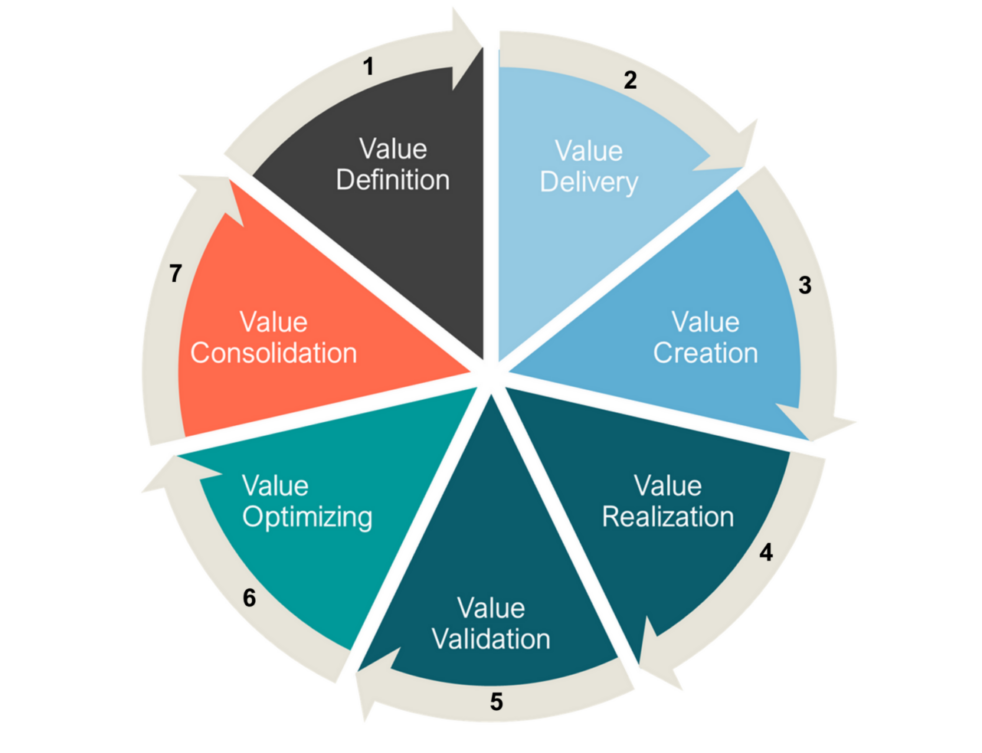
We explore the evolution of Microsoft's channel strategy over the past ten years, and what can be learned by viewing it through a Value Cycle lens.

Guides and eBooks
The Microsoft Fabric Partner Guide curates our recent articles, videos and resources to accelerate Crayon partner learning.

Blogs
An explosion in ransomware attacks has fueled a nationwide review of the issue, as concern rises that secret payoffs add increased fuel to the cybercrime fire.

Webinars Series
How do security assessments empower your cybersecurity practice to respond to the rise of AI? Find out!


Case Studies
Essential Eight Compliance can be tough to maintain for partners and customers. Learn how Airlock simplified the challenge for one MSP, and delivered faster time to value.

Press Release

Podcast
Cybersecurity experts from Crayon, SMX and Red Sift cover the realities of the complex threat landscape and how partners can respond.

Company Announcements

Press Release
Empowering Partners, MSPs and ISVs with best-in-class protective DNS security solutions

Blogs
Crayon cloud security assessments help partners lock down M365 and Azure environments and build profitable cybersecurity practices. Learn how.


Connect Data Protection to strategic objectives via this Whitepaper

What are the most critical business objectives and solution adoption priorities for SMBs in our region? Download the latest Forrester study to find out!

Our APAC channel business is now part of a global organisation. That means there is a whole new world of value on offer for our partners. We can help you to tap into all of it.